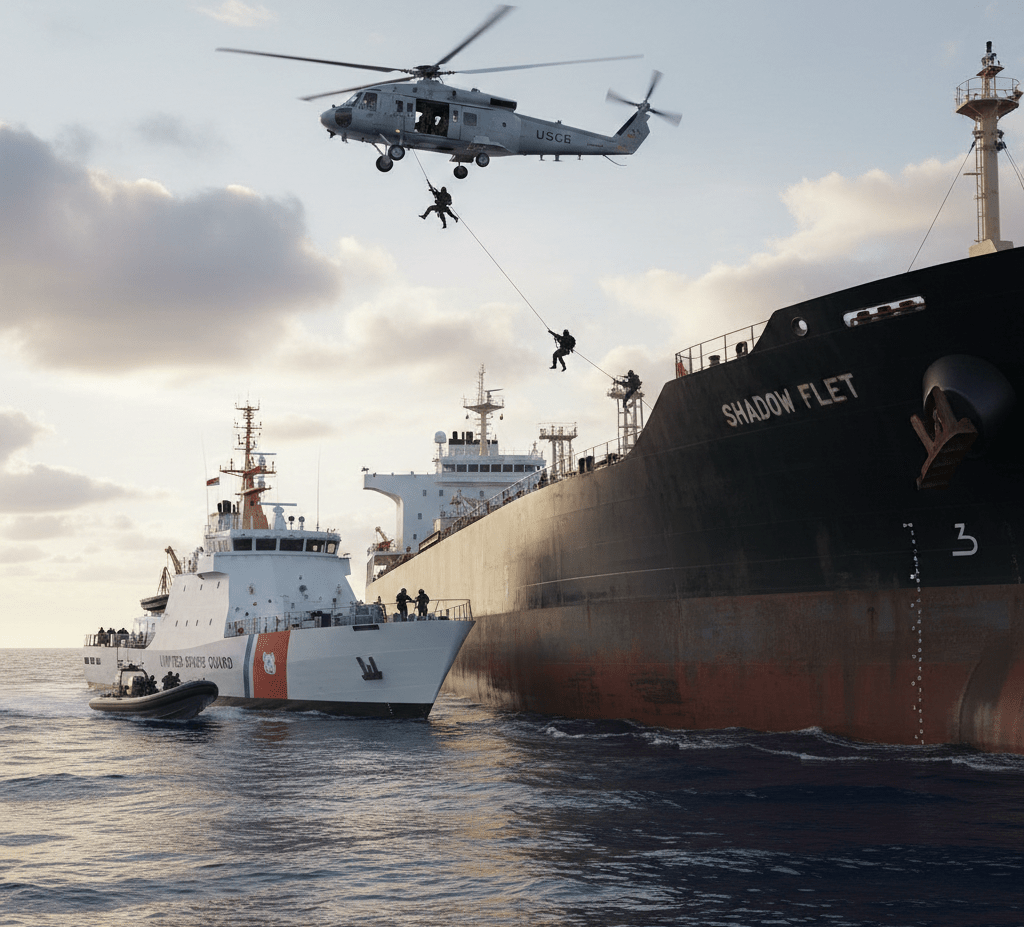
The U.S. Navy just completed one of the most dramatic maritime operations in recent memory, seizing the shadow fleet tanker Aquila II after a 10,000-mile pursuit across the Indian Ocean. This high-stakes chase has captured attention from shipping industry professionals, maritime security analysts, and anyone following global trade enforcement efforts.
Shadow fleet vessels like Aquila II operate in legal gray areas, often helping countries circumvent international sanctions by transporting oil and other goods without proper documentation. This particular case shows how far authorities will go to crack down on these elusive operations.
We’ll break down what shadow fleet operations actually involve and why they’re such a big deal for international trade. You’ll also get the full story behind the Aquila II case, including details about the epic chase that spanned thousands of miles of open ocean. Finally, we’ll look at what this seizure means for maritime security moving forward and how it might change the game for similar operations worldwide.
Understanding the Shadow Fleet Operations

What shadow fleets are and how they operate
Shadow fleets represent a sophisticated network of vessels deliberately designed to operate below the radar of international maritime monitoring systems. These tankers, cargo ships, and other maritime vessels typically begin their covert operations by disabling or manipulating their Automatic Identification Systems (AIS), effectively making them invisible to standard tracking technologies. The ships often employ deceptive practices such as ship-to-ship transfers in remote ocean locations, where cargo changes hands between vessels far from port authorities and surveillance systems.
The operational structure revolves around creating multiple layers of obscurity. Vessels frequently change flags, ownership structures, and even names to avoid detection. Many shadow fleet operators establish shell companies across different jurisdictions, making it nearly impossible to trace actual ownership back to sanctioned entities. These ships often carry outdated or falsified documentation, and crews may operate under fake identities or incomplete records.
Countries and entities that utilize these covert maritime networks
Several nations have developed extensive shadow fleet capabilities to circumvent international sanctions and trade restrictions. Russia has dramatically expanded its shadow fleet operations following sanctions imposed after the 2022 invasion of Ukraine, with estimates suggesting over 400 vessels now operate in this capacity to transport crude oil and petroleum products. Iran pioneered many shadow fleet techniques during decades of sanctions, developing expertise in covert oil exports that other nations later adopted.
North Korea maintains a smaller but highly active shadow fleet primarily focused on coal exports and fuel imports, despite comprehensive UN sanctions. Venezuela has also relied on shadow vessels to export oil while facing U.S. sanctions. Beyond state actors, criminal organizations and private entities exploit these networks for smuggling operations, arms trafficking, and other illicit activities. Insurance companies, shipping brokers, and financial institutions sometimes knowingly or unknowingly facilitate these operations through complex legal structures.
Economic impact of shadow fleet activities on global trade
Shadow fleet operations distort global commodity markets by creating artificial supply constraints and price volatility. When major oil producers resort to covert shipping methods, legitimate market participants struggle to accurately assess supply levels, leading to unpredictable price swings that affect everything from gasoline costs to shipping rates worldwide. The International Energy Agency estimates that shadow fleet activities account for millions of barrels of oil moving outside official channels daily.
These operations undermine fair competition by allowing sanctioned entities to sell commodities at below-market rates, since they avoid regulatory compliance costs and insurance premiums. Legitimate shipping companies face unfair competition from vessels operating without proper insurance, safety certifications, or environmental protections. The practice also reduces transparency in global supply chains, making it harder for companies to ensure their operations comply with sanctions and environmental standards.
Methods used to evade international detection and sanctions
Modern shadow fleet operators employ increasingly sophisticated evasion techniques. AIS manipulation has become an art form, with vessels broadcasting false positions, switching transponder signals between ships, or creating “spoofed” locations that place them thousands of miles from their actual position. Some ships install multiple AIS systems, allowing them to switch between legitimate and false identities depending on their location and cargo.
Ship-to-ship transfers have evolved into complex choreographed operations. Vessels rendezvous in international waters, often in areas with minimal maritime patrol presence, such as remote sections of the South China Sea or off the coast of West Africa. During these transfers, both vessels typically disable their tracking systems and may use smaller boats to ferry cargo, making detection even more challenging.
Financial evasion techniques include using cryptocurrencies for transactions, establishing payment systems through non-sanctioned countries, and creating complex ownership structures that span multiple jurisdictions. Some operators maintain legitimate front businesses that provide cover for illicit activities. Insurance fraud has become common, with vessels carrying minimal or fake coverage while claiming full protection to port authorities.
Physical modifications to vessels also play a role. Some ships alter their appearance between voyages, changing paint schemes, removing or adding structures, and even modifying their names and registration numbers. Advanced operations may involve installing hidden compartments or using specially designed cargo holds that can conceal the true nature of their contents during inspections.
The Aquila II Tanker Case Details

Vessel Specifications and Operational History
The Aquila II operates with a deadweight capacity of approximately 159073 tons, for covert operations. Built in 2004 at a South Korean shipyard, the vessel initially served legitimate commercial routes before changing hands multiple times through shell companies registered in various flag-of-convenience jurisdictions.
The tanker’s technical specifications reveal sophisticated modifications that raised red flags among maritime intelligence agencies. Advanced GPS spoofing equipment allows the vessel to transmit false location data, while specialized cargo handling systems enable ship-to-ship transfers in international waters without port infrastructure.
Records show the Aquila II underwent significant retrofitting in 2022 at a facility in Malaysia as reported.
Suspicious Activities That Triggered the Investigation
Intelligence agencies first noticed unusual patterns when the Aquila II began executing a series of seemingly random course changes across multiple ocean basins. Satellite imagery captured the vessel conducting nighttime rendezvous with unidentified ships in remote areas of the Arabian Sea, well beyond established shipping lanes.
The investigation intensified after port authorities in Oman reported discrepancies in the vessel’s cargo manifests. While documents declared the ship was carrying refined petroleum products, chemical analysis of residual samples suggested the presence of crude oil with markers consistent with sanctioned sources.
Financial tracking revealed suspicious payment patterns involving cryptocurrency transactions and hawala networks that bypassed traditional banking systems. The vessel’s operating company showed connections to entities previously sanctioned for facilitating illicit oil trades, creating a web of shell corporations designed to obscure ownership and operational control.
Most damning was the discovery of AIS (Automatic Identification System) manipulation, where the vessel transmitted false identification codes and position data for extended periods. During one three-week stretch, the Aquila II appeared simultaneously in satellite imagery near the Strait of Hormuz while its AIS signal placed it 800 miles away in the Indian Ocean.
Route Analysis and Ports of Call During the Pursuit
The chase began when the Aquila II departed from an anchorage near Fujairah in the UAE, initially heading southeast toward the Indian Ocean. Maritime patrol aircraft tracked the vessel as it maintained radio silence and disabled its transponders approximately 200 nautical miles from the Omani coast.
Analysis of the vessel’s route reveals a calculated strategy to exploit gaps in international maritime surveillance. The ship followed a zigzag pattern through international waters, staying just outside the territorial limits of multiple nations while avoiding heavily monitored shipping corridors.
| Location | Distance Covered | Key Activities |
|---|---|---|
| Arabian Sea | 2,400 miles | Initial evasion maneuvers |
| Central Indian Ocean | 3,200 miles | Deep water hiding |
| Bay of Bengal approaches | 2,800 miles | False destination signals |
| Sri Lankan waters | 1,600 miles | Final interception zone |
The vessel made no official port calls during the pursuit, instead relying on pre-positioned supply ships for fuel and provisions. Coast guard intercepted communications revealed attempts to arrange emergency port access in Madagascar and the Seychelles, both of which were denied following diplomatic pressure from U.S. authorities.
Forensic analysis of the ship’s navigation systems later revealed pre-programmed waypoints suggesting the crew had planned multiple escape routes, including potential runs toward Somalia’s lawless coastline or remote Indonesian archipelago waters where enforcement capabilities remain limited.
The Epic 10,000-Mile Maritime Chase

Initial Detection and Tracking Methods Employed
The pursuit of the Aquila II began when intelligence analysts at the U.S. Maritime Administration flagged unusual transponder activity in Southeast Asian waters. The tanker had switched off its Automatic Identification System (AIS) while entering what appeared to be a routine port call, but satellite imagery revealed the vessel conducting suspicious ship-to-ship transfers in international waters.
Coast Guard intelligence officers cross-referenced the vessel’s movements with known sanctions violations, discovering a pattern of deceptive shipping practices. The tanker had been using multiple fake identities, switching between different vessel names and flags of convenience to avoid detection. Maritime tracking specialists noticed the ship’s unusual route deviations and extended periods of radio silence, classic indicators of shadow fleet operations.
Radar stations across the Indian Ocean began coordinating their surveillance efforts, creating a digital net that would make it nearly impossible for the vessel to disappear completely. The initial detection phase relied heavily on commercial satellite feeds and maritime domain awareness systems that could spot vessels even when they attempted to go dark.
International Cooperation Between Naval Forces
The chase required unprecedented coordination between multiple naval commands across three major ocean regions. The U.S. Fifth Fleet, operating from Bahrain, served as the primary command center, but success depended on real-time intelligence sharing with allied nations.
Indian Navy vessels provided crucial support in the western Indian Ocean, sharing radar data and positioning their patrol ships along likely escape routes. British Royal Navy assets stationed in Diego Garcia contributed surveillance aircraft and maritime patrol capabilities, extending the operational reach of the pursuit team.
French naval forces operating from their base in Djibouti offered logistical support and additional surveillance assets. The cooperation extended beyond traditional allies – even nations with limited naval capabilities provided port access and refueling stations for pursuing vessels.
Communication between these diverse naval forces required secure satellite links and standardized reporting protocols. Daily briefings occurred across multiple time zones, with intelligence officers from different nations working around the clock to maintain continuous tracking of the target vessel.
Challenges Faced During the Extended Pursuit
Weather conditions in the Indian Ocean presented the first major obstacle. Monsoon seasons created massive storm systems that could easily hide a vessel from satellite surveillance and make aircraft operations dangerous. The pursuing forces had to work around seasonal weather patterns while maintaining constant pressure on their target.
The Aquila II’s crew demonstrated sophisticated evasion techniques, including running at reduced power to minimize their heat signature and traveling in shipping lanes crowded with legitimate commercial traffic. They attempted to blend in with regular cargo vessels, making visual identification extremely difficult for patrol aircraft.
Fuel and supply logistics became critical issues as the chase extended across vast ocean distances. Naval vessels needed regular refueling, which meant coordinating with supply ships and potentially losing contact with the target during resupply operations. The extended timeline also strained crew resources and required rotating personnel to maintain operational effectiveness.
Legal jurisdictional questions arose as the vessel crossed through different nations’ territorial waters. Each transit required diplomatic clearance and coordination with local maritime authorities, sometimes causing delays in the pursuit operation.
Advanced Surveillance Technologies Used in the Operation
Synthetic Aperture Radar (SAR) satellites played a central role in maintaining contact with the vessel even during periods of poor weather or darkness. These systems could penetrate cloud cover and provide detailed imagery of ships on the ocean surface, making it nearly impossible for the Aquila II to completely disappear.
Maritime patrol aircraft equipped with advanced electro-optical sensors conducted regular overflights, capturing high-resolution images and video footage of the suspect vessel. These aircraft could stay on station for extended periods and relay real-time intelligence back to command centers.
Underwater surveillance networks detected the vessel’s acoustic signature, allowing tracking even when surface surveillance was compromised. Ocean-bottom hydrophone arrays, originally designed for submarine detection, proved valuable for monitoring surface vessel movements across vast distances.
Artificial intelligence algorithms processed massive amounts of maritime traffic data, identifying patterns and predicting likely routes for the fleeing vessel. Machine learning systems analyzed historical shipping data to anticipate where the Aquila II might attempt to seek refuge or conduct additional transfers.
Commercial shipping databases were continuously cross-referenced with real-time vessel positions, helping identify when the target ship attempted to assume false identities or blend in with legitimate traffic. This data fusion approach created a comprehensive picture of maritime activity across the entire pursuit area.

The Aquila II seizure shows how determined the U.S. is to crack down on shadow fleet operations that help countries dodge sanctions. This 10,000-mile chase across the Indian Ocean proves that even the most elaborate schemes to hide oil shipments can’t escape international law enforcement. The case highlights the sophisticated networks these tankers use to move sanctioned oil and the equally advanced tracking methods authorities deploy to stop them.
For shipping companies and oil traders, this seizure sends a clear message: the costs of participating in shadow fleet operations far outweigh any short-term profits. The legal framework supporting these seizures continues to strengthen, making it harder for rogue operators to hide behind shell companies and false documentation. Anyone involved in maritime trade should take note – transparency and compliance aren’t just good business practices anymore, they’re essential for survival in an increasingly monitored global shipping environment.
Leave a comment